先进的产品品质、全新的管理模式、前瞻的技术研发和完善的服务

化工泵依靠离心原理来抽取液体物料,特殊材料制成的化工泵适用于瓶、桶、缸、池或其他容器中抽取腐蚀性液体。 1)化工泵广泛应用于化工、石油、冶金、轻工、合成纤维、环保、食品、医药等部门…
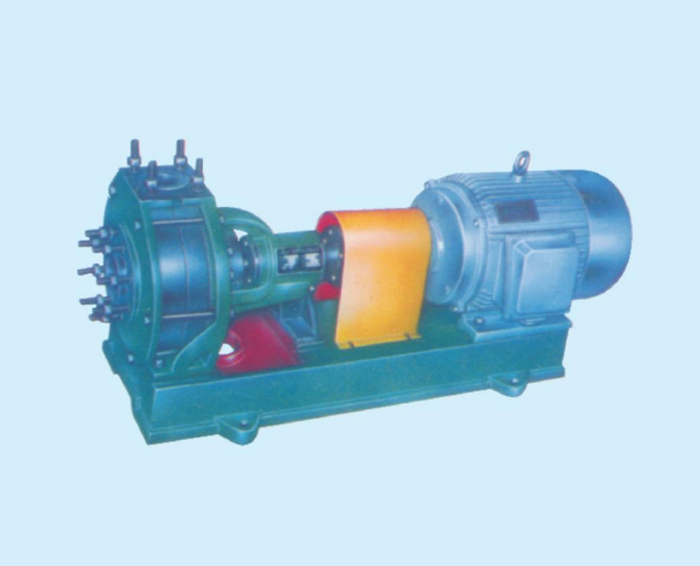
石油化学工业在国民经济中占据非常重要的位置,化工流程泵作为关键配套设备也越来越受到人们的关注。由于化工介质的特性错综复杂,加之用户的要求不断提高,作为生产厂家,我们应如何选型?应*点…
公司始终秉承“踏实、拼搏、担当”的企业精神,一切从客户的需求出发,以先进的产品品质、全新的管理模式、前瞻的技术研发和完善的服务配套,为客户不断提供价值和感动,开拓行业、影响未来。
联系我们